Setting up a Secondary AI-Hunter Console for Disaster Recovery
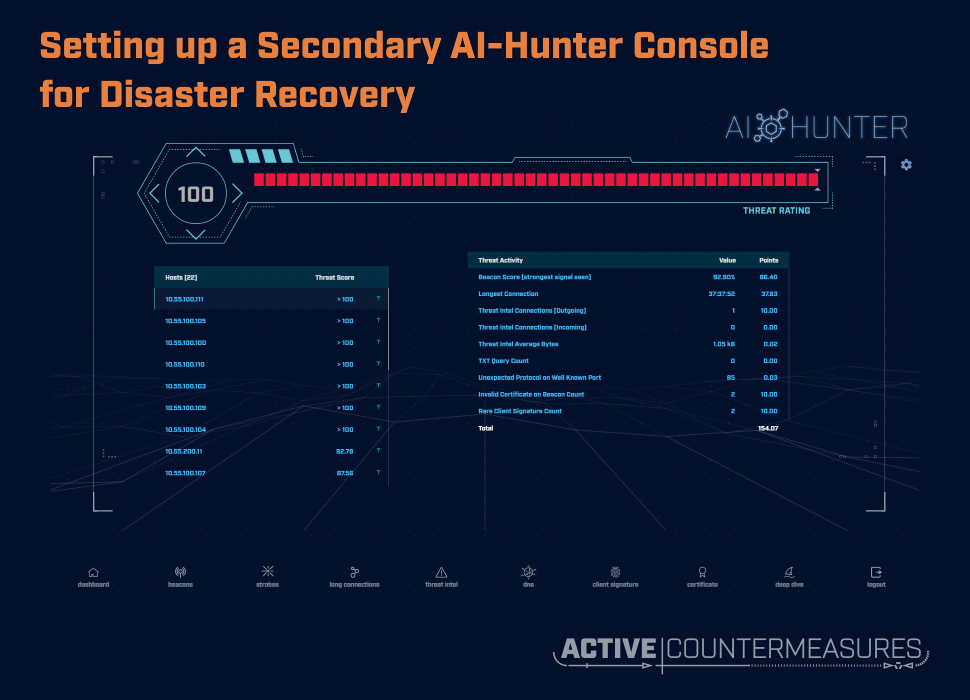
Setting up a second AI-Hunter console
AI-Hunter is licensed under a site license – there are no additional costs for having more than one AI-Hunter console. This allows you to have two systems ingesting the same data.
You’ll need a second computer to run AI-Hunter with similar system specs. If you don’t have a dedicated disaster recovery site, you could use a virtual machine at a cloud provider. Make sure that no matter where you place your secondary AI-Hunter system, your sensors need to be able to ssh to it; if that requires a VPN, think through what happens if that VPN is unavailable.
Once you have a physical or virtual system with a supported operating system, run the AI-Hunter installer a second time and install it to the new system. You’ll only be installing AI-Hunter to the new system – you do not need to install anything to any of your sensors.
Sending all logs to both consoles
On each of your sensors, edit the file /etc/cron.d/bro_log_transport (substitute your favorite editor):
sudo vim /etc/cron.d/bro_log_transport
You’ll see a line like:
5 * * * * bob /usr/local/bin/bro_log_transport.sh --dest aihunter.example.com
(Your line will differ and may have extra parameters; the above is just an example.)
Make an exact duplicate of the line you see, then edit the destination hostname to be the hostname or IP address of the new console:
5 * * * * bob /usr/local/bin/bro_log_transport.sh --dest aihunter2.example.com
Make sure you end up with exactly two lines, the original and the duplicate, each on a single line in the file.
If you’re not currently logged in as the user-specified (“5 * * * * bob /usr/…”), log out and log back in as that user. Now run bro_log_transport by hand:
/usr/local/bin/bro_log_transport.sh --dest aihunter2.example.com
Accept the ssh host key if prompted, and provide the data import user’s password to send over the private key that will be used for all future transfers. The script should send over the last three days of bro logs; these will be automatically imported into the new AI-Hunter console at the top of the hour.
Whitelist download and upload
After you do the installation, and whenever you make changes to your whitelist in one of the consoles, make sure you:
- Download the whitelist to your laptop. To do this, go to the Dashboard tab, click on the gear in the upper right, select whitelist, and choose “Download whitelist”. (For reference, this will download “whitelist.json” to your browser’s download directory; you may want to make a dated copy of this.)
- Upload the whitelist to the other console. Go to the Dashboard tab, click on the gear in the upper right, select whitelist, and choose “Upload whitelist”. You’ll be asked to select a file; pick the whitelist file that was just downloaded. The entries you send up will be merged with any that are already there.
New versions of AI-Hunter
When it comes time to upgrade your original AI-Hunter console with a new version, make sure you run the installer twice, once for each console.

Bill has authored numerous articles and tools for client use. He also serves as a content author and faculty member at the SANS Institute, teaching the Linux System Administration, Perimeter Protection, Securing Linux and Unix, and Intrusion Detection tracks. Bill’s background is in network and operating system security; he was the chief architect of one commercial and two open source firewalls and is an active contributor to multiple projects in the Linux development effort. Bill’s articles and tools can be found in online journals and at http://github.com/activecm/ and http://www.stearns.org.