espy
Network Monitoring Without a Network Sensor!
About espy
AC-Hunter makes it easy to detect threats on your network, but what happens when your workforce is scattered geographically? With the uprise in the number of work-from-home employees, the challenge of protecting all devices in your organization becomes even more difficult. Where would you be able to put a centrally-located network sensor? Wouldn’t it be costly to place a sensor in every remote employee’s home network? Whoah, hold on… what are the privacy issues involved with monitoring home networks?
No worries, we already have answers to those questions. Espy collects network traffic from Windows systems regardless of geographical location. The network traffic is then stored as Zeek logs on a server of your choosing. The traffic can also be forwarded to an Elasticsearch instance.
Primary Features
- Collects network traffic from Windows hosts which have the espy agent installed
- Transforms collected traffic into Zeek logs as if all traffic was one virtual network sensor
- Logs are stored on one centralized server
- Optionally send traffic to an Elasticsearch instance
Using espy with RITA
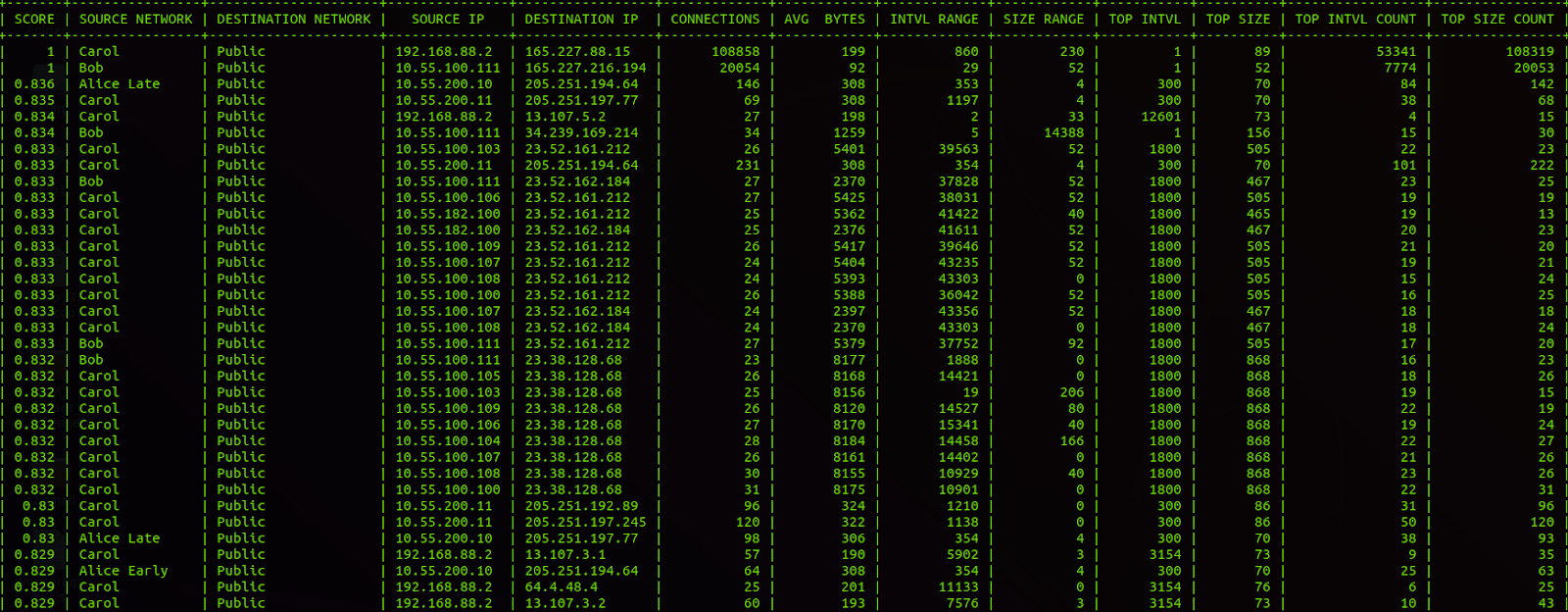
Any Zeek logs created by espy can be analyzed with RITA. Imported datasets with these logs have the NetBIOS name of the source and destination of the connection so that each host is distinguishable across different networks. Analysis of espy’s Zeek logs will produce results for beacons, strobes, and long connections.
Using espy with AC-Hunter
When espy is installed along AC-Hunter, all of the network traffic made by your remote hosts is analyzed and made available in AC-Hunter for beacons, strobes, and long connections. All logs created by espy are imported along with the standard Zeek logs. The NetBIOS names for hosts running the espy agent will appear along with the host’s IP, making it possible to distinguish which remote host an IP belongs to.
The NetBIOS name is available for a top-scoring host running the espy agent.
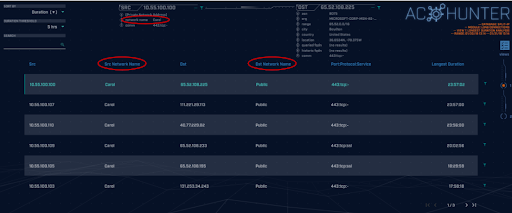
We can see the NetBIOS name for the source host of a beaconing connection.
We can see the source and destination NetBIOS names for long connections.
Download Details
As part of our ongoing commitment to free and open-source software, we’ve made both espy and the espy Windows agent open source.
Download espy: https://github.com/activecm/espy
Additional Resources
Blog Posts:
Espy – Network Monitoring Without a Network Sensor!