Wireshark For Network Threat Hunting: Creating Filters
Let’s say you have a system you believe to be compromised. And, let’s say you can get a packet capture from that system. Specifically, we want to have a packet capture of the traffic from that system that is leaving your network going out to the Internet. We also call this egress traffic. In this post, we will be looking at how to identify the connections with the most packets, how to enable DNS resolution in the captures, and how to create a series of basic filters to remove known “good” traffic from the packet capture.
One of the more powerful techniques for network hunting is sifting through a network capture. At least, that is what everyone says. Then, you open a 2GB network capture in Wireshark, excited to be one of the “leet” few who use this powerful tool and you get this…
So, yea. What next?
Let’s dive in.
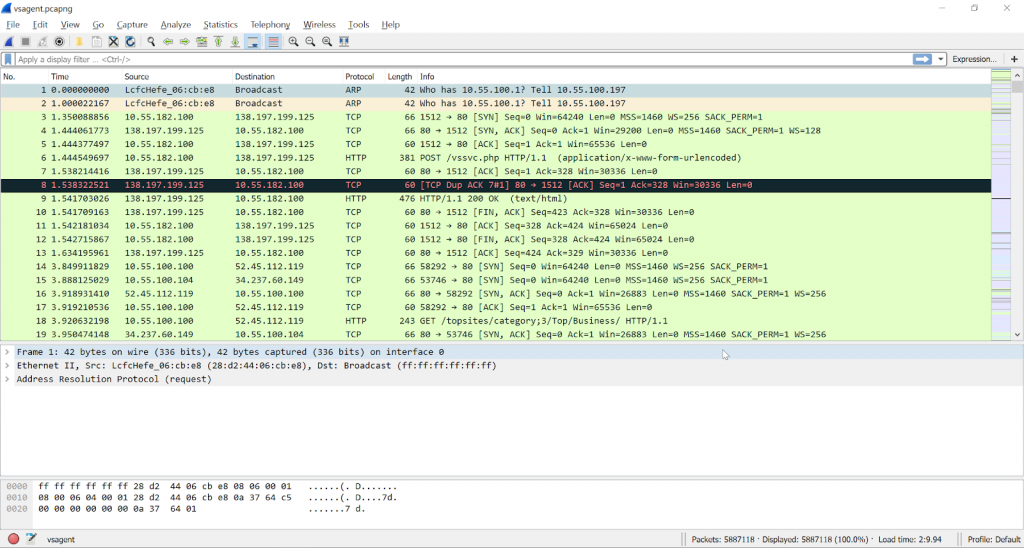
The top pane is all of the individual packets it has the number of the packet, the time, the source, destination, protocol, length and other information. Take a moment and click on any packet in your capture.
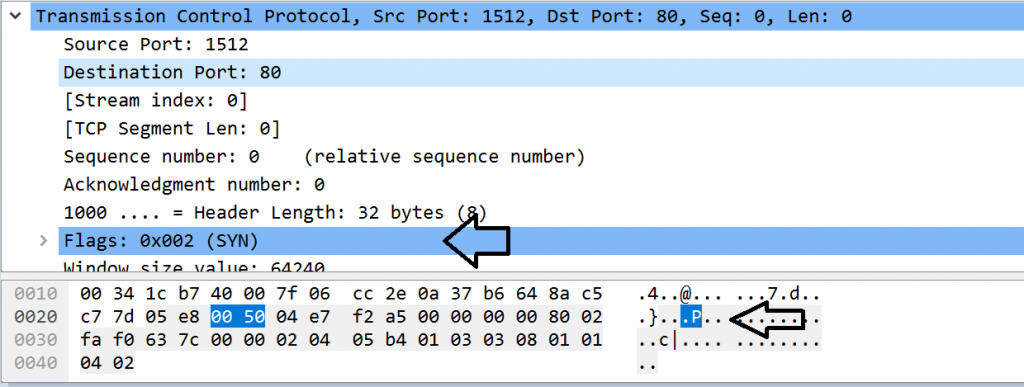
When you select a packet the second and third pane will change. The third pane is the raw hex and ASCII decode of the packet and the second pane describes what that hex means. After all, we are all not Chris Brenton, Bill Stearns, Mike Poor or Judy Novak. We can’t read raw hex… Yet…
When you select some hex in the third pane or a section in the second pane it will highlight the corresponding information in the other pane.
Now, let’s leave that be for a bit and play with some filters.
You can see the filter box at the top of the screen.
This is, without question, the most powerful part of Wireshark. The ability to filter out and focus in on conversations in the TCP stream is what we tend to do when looking for evil on the wire.
Let’s start by looking at some statistics and have Wireshark create a filter for us.
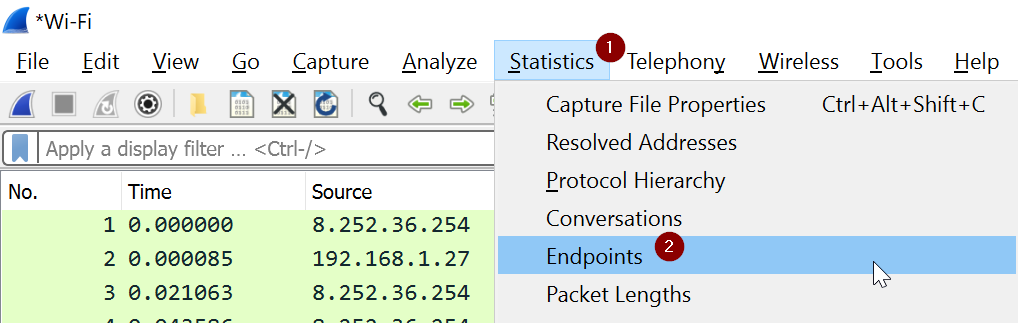
Please select Statistics and Endpoints:
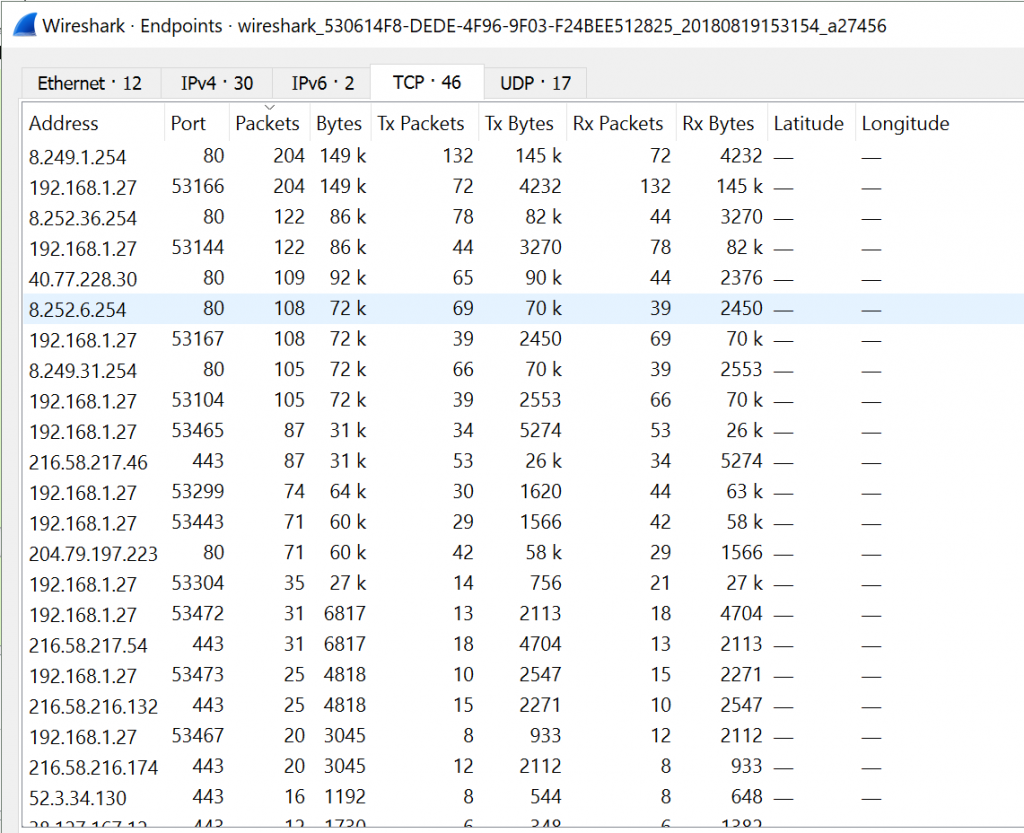
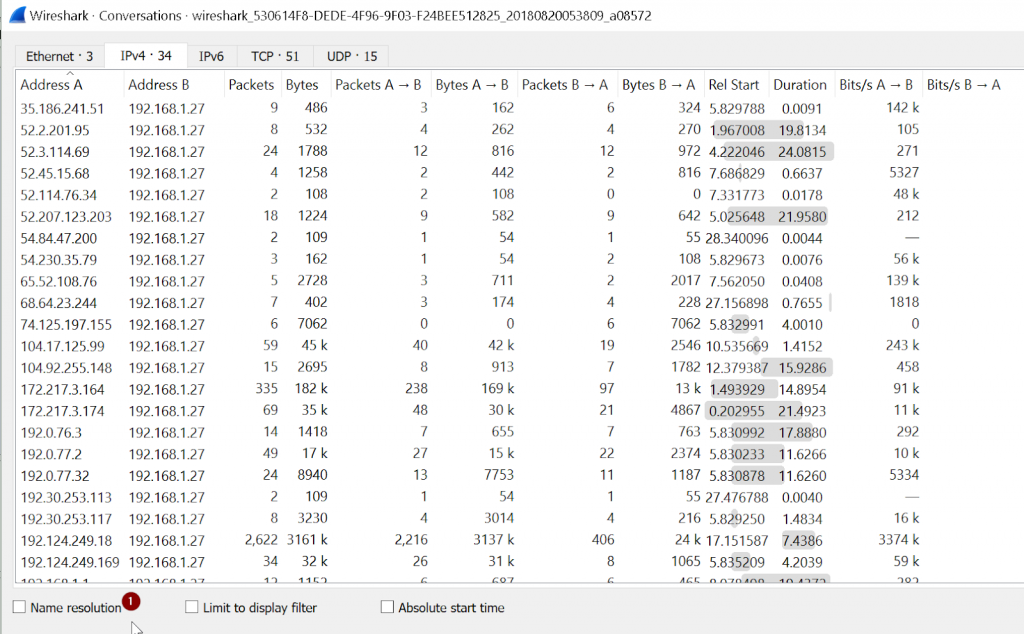
This will show all the endpoints in the capture. When working through these captures it is helpful to start with the endpoints that have the most packets and work your way down. It is a way of breaking out signal to noise. Now, please do not take this to mean this is the only way to approach a packet capture looking for malware. It is just one way. We will cover other approaches over other posts.
Another way to view the data is by “Conversations”.
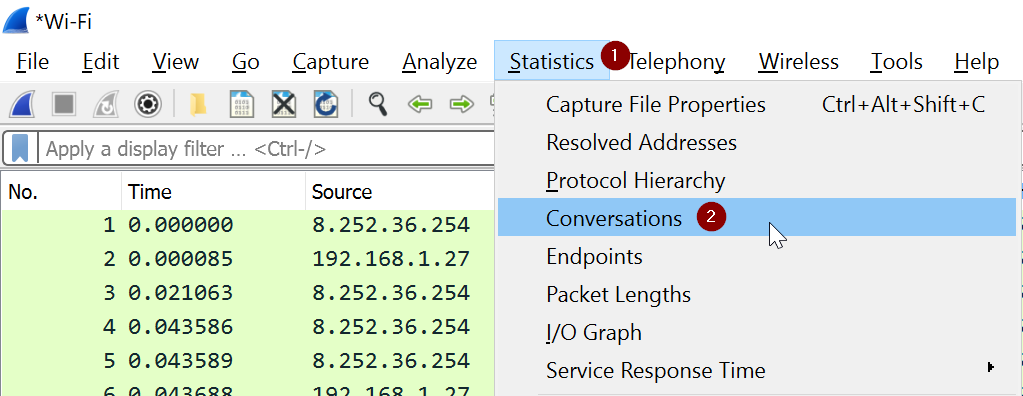
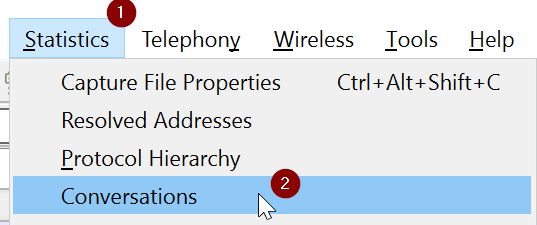
Please select “Statistics” then “Conversations”.
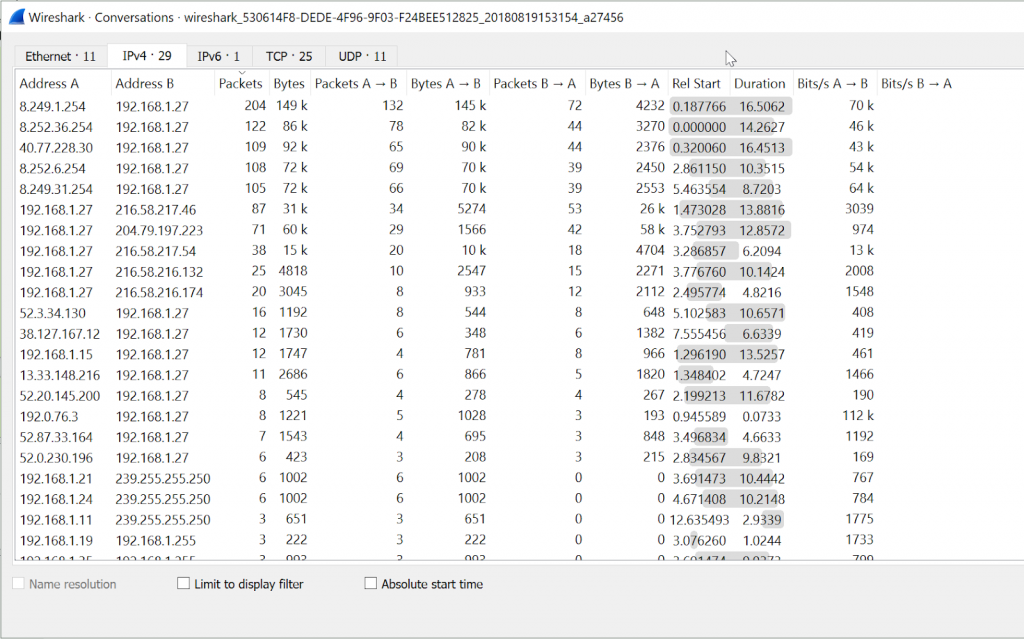
Whenever I think there is a system that is compromised, I can pull this up and see which other systems the “suspect” system is communicating with. In a bit we are going to start filtering these conversations out of the stream.
Now, I would like you to look at the fact that all the IP addresses are just that, IP Addresses. Also, notice that the Name Resolution box is greyed out. Let’s enable that now.
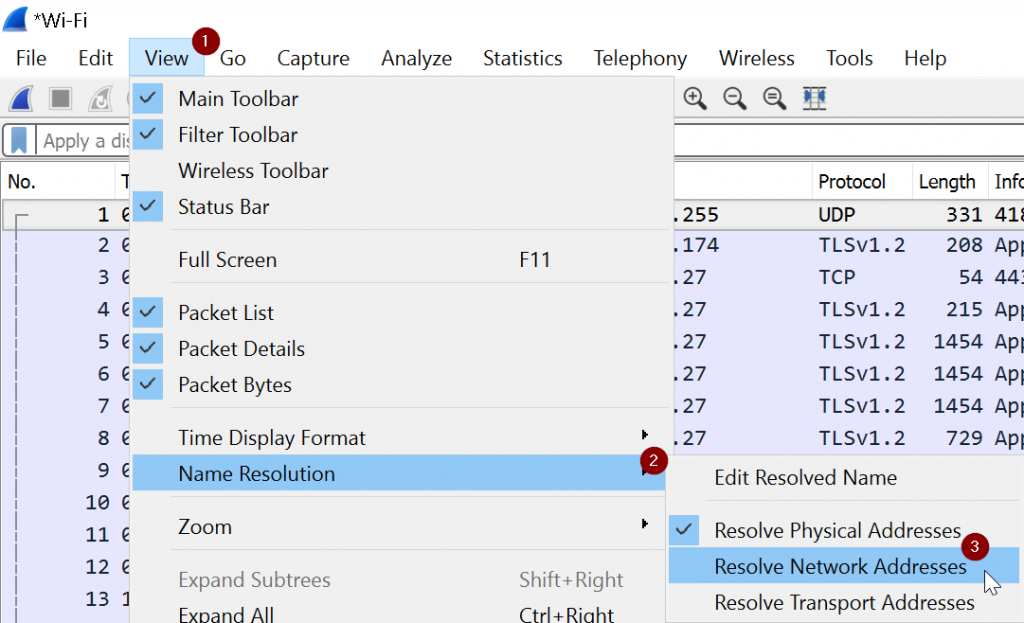
Please close the Conversations window and go back to the main Wireshark window. Now, select View > Name Resolution and select Resolve Network Addresses and Resolve Transport Addresses.
Now, select Statistics > Conversations:
And you should see all of the different IP Conversations. But look, resolve IP addresses is no longer grayed out!
Now, you can see the resolved host names:
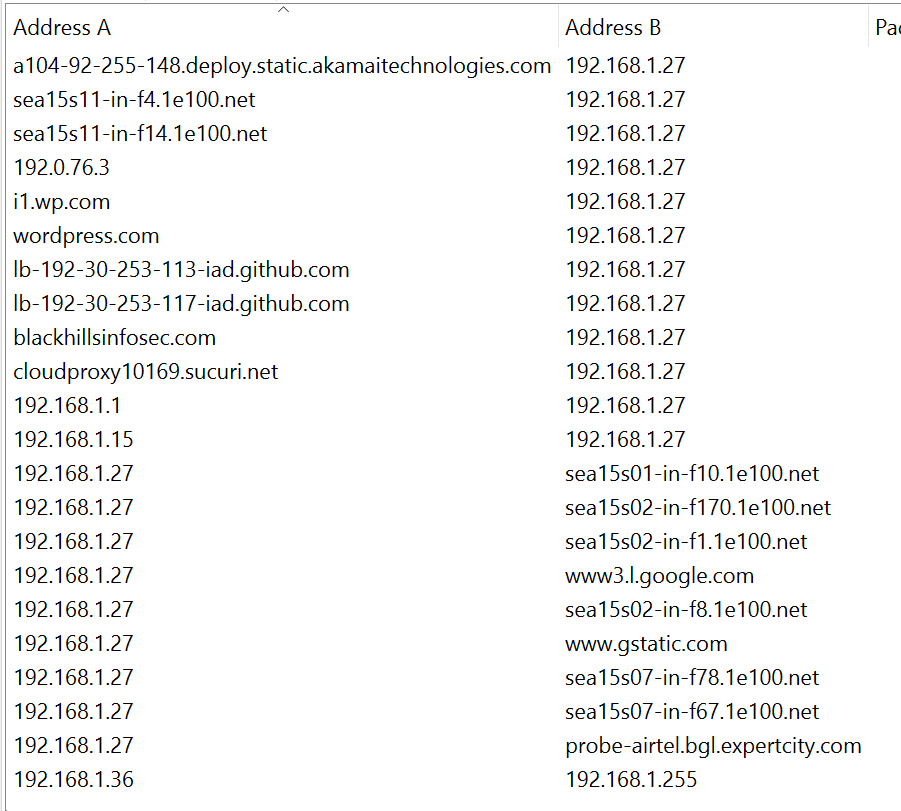
This is helpful for filtering out traffic that is not evil and trying to sift down to something “interesting.”
Now, let’s create some filters!
Move the conversations screen to the side, and have the main Wireshark screen on another side.
Now, select the IPv4 tab and sort the data by Packets:
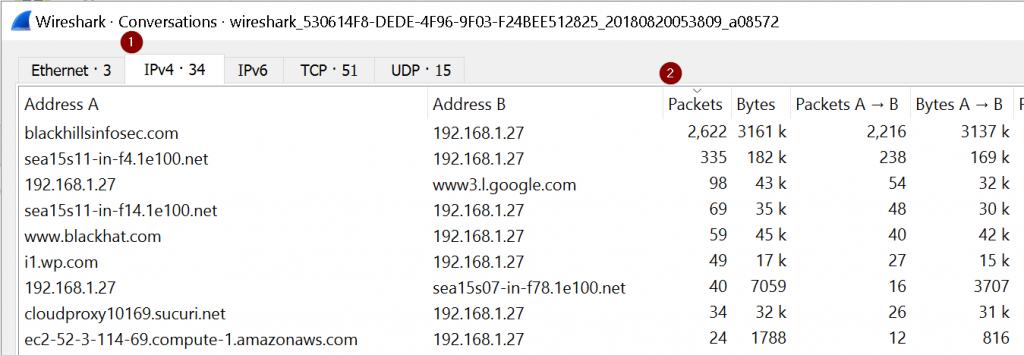
The goal here is to sift out as much traffic as possible. We see that there are a lot of packets to blackhillsinfosec.com and Google. Let’s filter those two out.
Now, move from the Conversations pane to the main Wireshark pane and put in the following:
!ip.host contains "blackhillsinfosec.com" && !ip.host contains "google.com"
Now, please note, your top talkers you want to filter will not be blackhillsinfosec.com or google.com. I am just using those for articulative purposes.
But look at what the filter did!
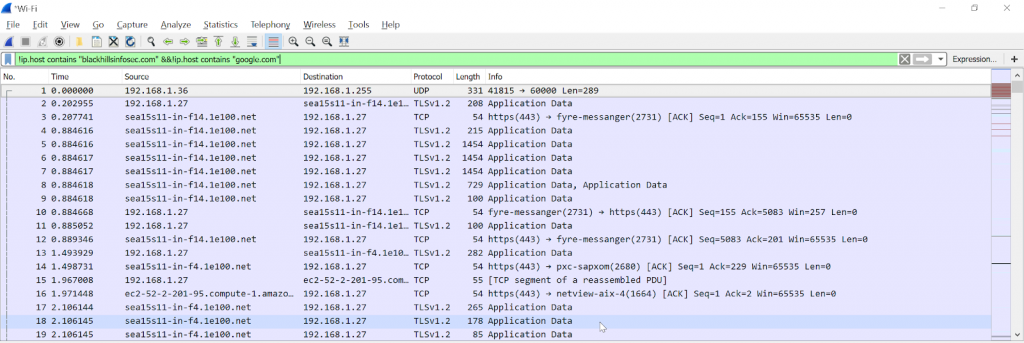
It removed all blackhillsinfosec.com and google.com traffic!
The goal is to keep filtering out traffic as you learn what that traffic is. Some endpoints are hard, CDNs, for example, are a nightmare.
For the next post we will look at some malware and filter till we find it!
See you next time!
John

John has both consulted and taught hundreds of organizations in the areas of security, regulatory compliance, and penetration testing. He is a coveted speaker and much loved SANS teacher. John is a contributor to the industry shaping Penetration Testing Execution Standard and 20 Critical Controls frameworks.