Detecting Domain Fronting Malware

There has been a lot of conversations lately in the offensive community about domain fronting and its imminent “demise”. There are a large number of different articles on how to set this up.
Below are some of my favorites:
Simplifying Domain Fronting by Tim Malcomvetter:
https://medium.com/@malcomvetter/simplifying-domain-fronting-8d23dcb694a0
What is Domain Fronting? By Finjan:
https://blog.finjan.com/what-is-domain-fronting/
And the MITRE writeup:
https://attack.mitre.org/techniques/T1172/
Why are we talking about it if it is “dead”? Well, I don’t think it is. There was a great presentation at SANS Hackfest by Matthew George @sircosec about how useful it is for the offensive community.
https://www.sans.org/event/pen-test-hackfest-2018/summit-agenda
And, we still are using it in on tests.
It may be a “violation of terms” and some of the big players may be getting rid of it. But, nothing dies on the Internet. We will keep seeing it for some time, even if some of the larger companies no longer support it.
So, let’s break it down. Basically, it is sending traffic to a “trusted” site or domain and that site forwards the traffic to the malicious C2 server.
Now, how do we detect something like that? Well, this is a much larger issue than just domain fronting. We need to be looking into how our tools and techniques relate to “trusted” sources. There are a large number of sites and domains your security tools ignore. For example, Gcat is a tool that uses well-formed email to communicate with implants. In researching this tool, we discovered that most firewalls and TLS/SSL interception tools ignore all traffic to Google. This issue of sites and companies that your tools blindly trust is a major issue.
Trust. Is a beautiful thing.
First, we need to stop ignoring these sites. This is one of the core reasons we like Bro/Zeek. It allows us to look at all traffic. And that is key. Then, of course, we will be using RITA.
Every so often, the BHIS testing team creates some malware for me to detect with RITA. They are getting pretty good at it. After all, it is their job.
The demo backdoor that Derek Banks created for this was a Cobalt Strike backdoor that used Domain Fronting. He also added in some beacon connection randomness… Because… Reasons.
![]() Below is a dump from our lab for 24 hours of the backdoor running:
Below is a dump from our lab for 24 hours of the backdoor running:
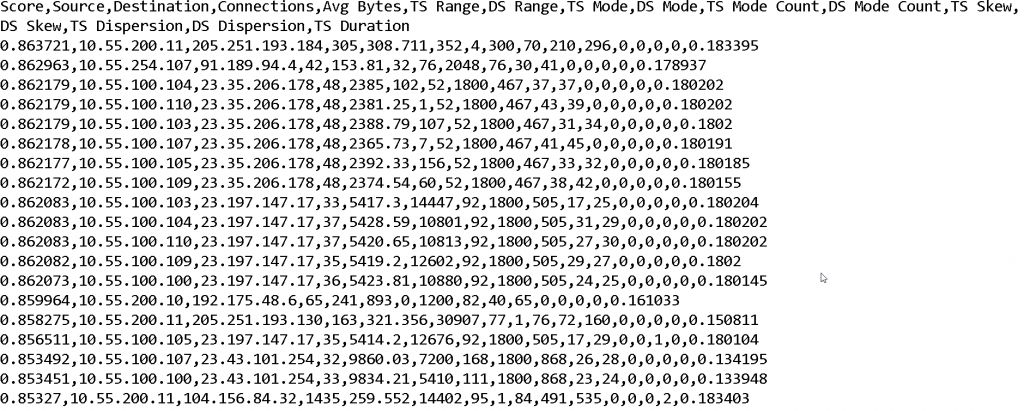
TRUNCATED##
First, don’t panic. I know this can be very overwhelming. In RITA we can get a better understanding of the .csv output with the -H flag.
![]()
This, at least, explains the different headers. I don’t use the above command except to better understand the columns.
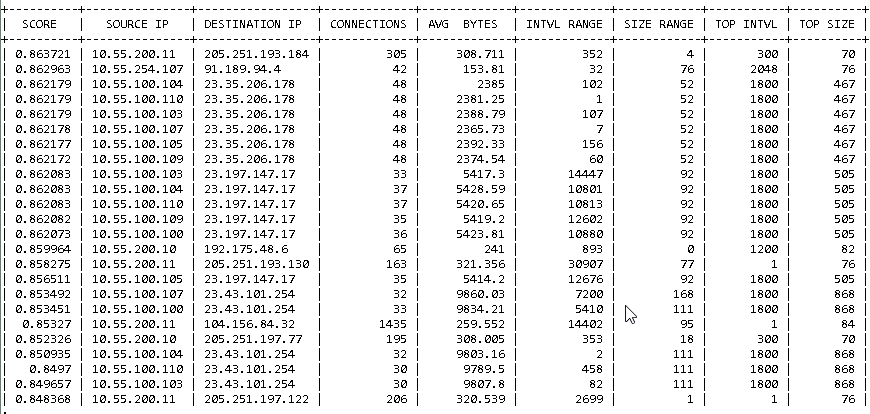
However, we can take the original output and load it into a spreadsheet – and do some sorting. This becomes critical when trying to find backdoors. We need to have the ability to couple multiple aspects of beaconing activity with things like blacklisting and attributes like connection count to refine the results.
Below is a spreadsheet where I did just that:
When I sort by connection count we get a result where the backdoor is much closer to the top. If we can sort by connection count and beacon score our backdoor is #2.
This means in order to catch some of these backdoors we need to have the ability to look at multiple aspects of malware together. The days of simple signature-based detection are over.
By the way, want to get started with RITA and Bro/Zeek? Check out RITA:
https://github.com/activecm/rita
Thanks!
John Strand
You still here? Good. I wanted to cover our free tools that help detect domain fronted C2. We are huge fans of open source at Active Countermeasures. That is why the core of what we do will always be free.
However, if you want a very cool UI to greatly speed up the process, then take a few moments to check out AI-Hunter. By the way, the AI stands for Actual Intelligence.
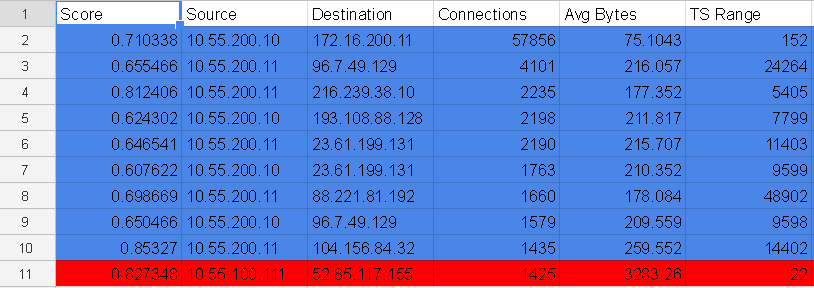
And, AI-Hunter helps bump these backdoors to the top of the research queue without the need to use external spreadsheets.
Below is the backdoor we covered detecting with RITA:
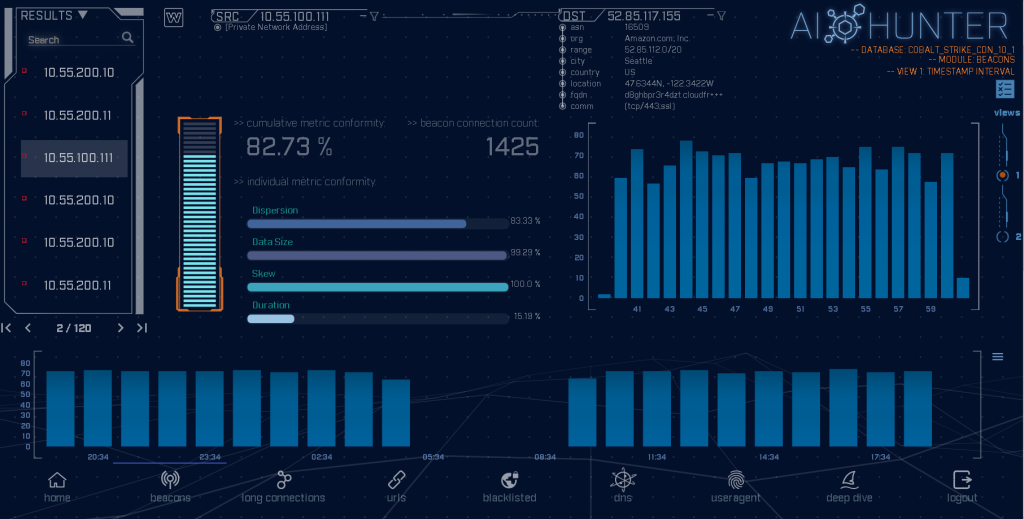
Notice that Derick added in a few more “features” that make this backdoor a bit more difficult to detect.
First, he randomized the connection interval:
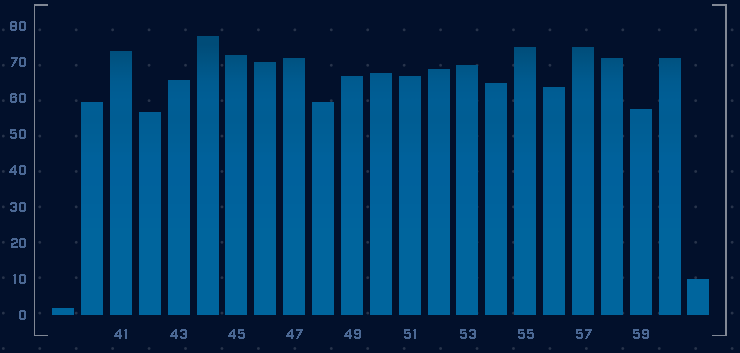
Second, he had the backdoor go “dormant” a few hours a day:

Finally, when we look at connections we bring a large number of different factors to the table to create a heads-up dashboard to bring backdoors like this to your attention:

We would love to set up a demo with you and your team. Just click here:
https://www.activecountermeasures.com/contact-us/
We are happy to talk about AI-Hunter or even answer general questions about network threat hunting and RITA.
Thanks!

John has both consulted and taught hundreds of organizations in the areas of security, regulatory compliance, and penetration testing. He is a coveted speaker and much loved SANS teacher. John is a contributor to the industry shaping Penetration Testing Execution Standard and 20 Critical Controls frameworks.