New Version in the Wild

Hey folks!
We released another new version of AI-Hunter last week. It’s been so crazy busy, I have not had a chance to announce it until now. There are some features in this release that have me super excited!
We’ve had some cosmetic changes to clean up the interface. Those will be apparent when you login. What I want to dive into here are the features that will make threat hunting your network that much easier. Let’s start by talking about ASN whitelisting.
I’ve discussed AI-Hunter’s whitelisting feature in the past. Along with all the other ways you can identify systems as trustworthy, you can now whitelist based on the Autonomous System Number (ASN) associated with the source or destination address of a session. As a use case example, consider Microsoft’s network. You are probably willing to trust any beacon like activity that takes place between internal systems and Microsoft’s patching servers. That’s expected behavior. However, you may have an entirely different opinion of Microsoft Azure, as anyone can spin up servers in that space.
Microsoft has 23 different ASNs to route traffic to different portions of their network. By whitelisting ASN 8075, you’ll trust all of Microsoft’s patching systems, even when they change IP address, without trusting system running in Azure. This is much easier than trying to whitelist based on IP or subnet!
There is a new reporting mode that lets you easily copy/paste information out of the user interface without all of the HTML code. This is handy when you need to Slack the info to a teammate or open a Jira ticket to get a forensic analysis performed.
Finally, we’ve added a feature to display the hostname a system was trying to reach when it generated the session. This is not a simple lookup of the IP address to see what hostname is associated with it (PTR query). We actually look at the DNS A or AAAA record query generated by the host and pull the name from that session. Here’s an example:
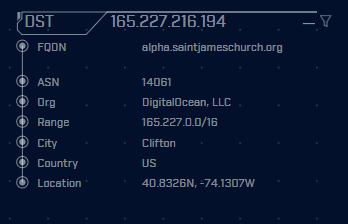
In this example, the IP address is part of a cloud hosting provider. So looking up the IP address is simply going to show us whatever name the hosting provider assigned. However because AI-Hunter is capturing the name server queries, we get to see the actual FQDN our internal system was attempting to reach. This can go a long way towards helping us identify if we are looking at malicious activity.
We have another release in the works so please stay tuned!

Chris has been a leader in the IT and security industry for over 20 years. He’s a published author of multiple security books and the primary author of the Cloud Security Alliance’s online training material. As a Fellow Instructor, Chris developed and delivered multiple courses for the SANS Institute. As an alumni of Y-Combinator, Chris has assisted multiple startups, helping them to improve their product security through continuous development and identifying their product market fit.