AI-Hunter v3.4 Has Been Released!

We’re pleased to send out the latest version of our flagship network analysis software, AI-Hunter! Our developers have put in overtime to take on customer requests and bug reports. This release is focused on usability improvements – things that simplify how you navigate and use AI-Hunter.
New Features
Investigation
One of the most common tasks when working with a particular IP address in AI-Hunter is getting more background about that IP address. We’d had limited ability to do that in previous releases, but with 3.4.0 that’s now spread throughout the entire interface. In the Beacons, Strobes, Long connections, Blacklisted, Client Signature, and Certificate tabs you can now click on an IP address to get a drop-down box that allows you to jump directly to one of 3 different references for IP address background information:
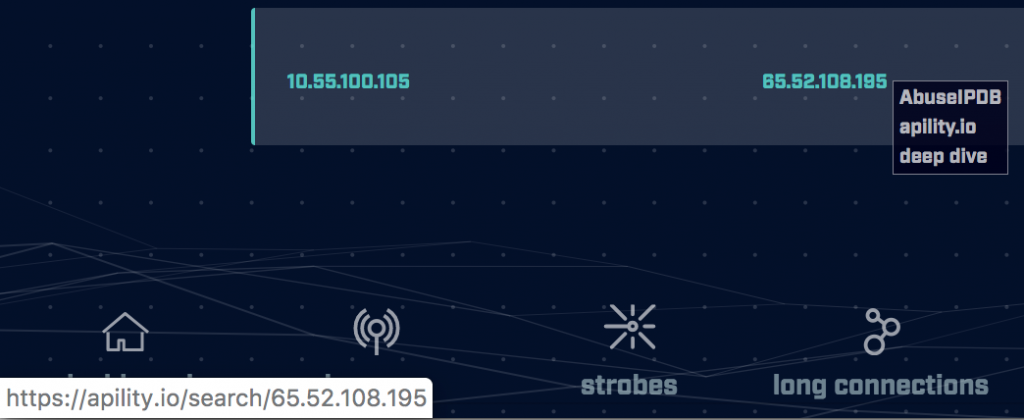
Even when the IP in question is an internal address (starting with 10., 192.168., or 172.16.-172.31.), you’ll still have a link to the deep dive module, so you can see that IP’s peers and the conversation types.
This means you won’t have to remember an IP and type it in by hand on the deep dive module, and since this happens so often, we hope it makes a more fluid experience for you.
Beacon Threshold
On the beacons tab, you can restrict your results to only those whose score is above a particular percentage:
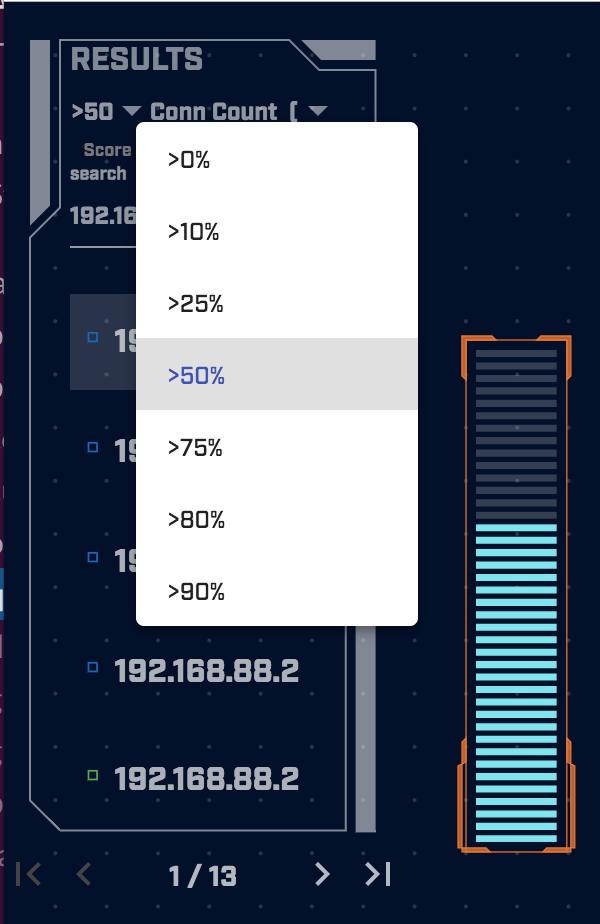
The sort type is also displayed in the results window just to the right of the “50”; in this example we’re sorting by Connection Count, descending.
Export
All tabs except the dashboard and deep dive now offer CSV export so you can pull out the details of the top 5 or top 50 results for import into other tools.
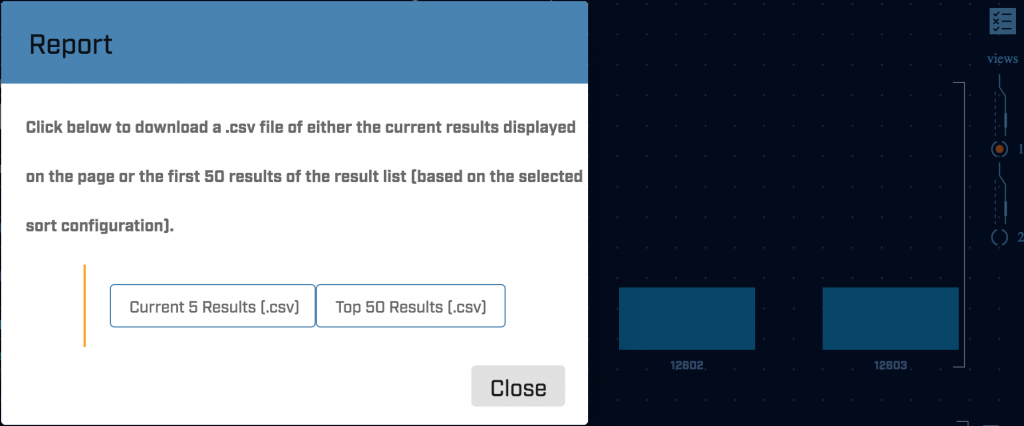
To see this option, click on the checklist icon in the upper right of those tabs.
Bug Fixes
Syslog Alerting
We made an incorrect design choice about how we thought the Syslog and Slack alerting would be used; we thought those using Syslog alerting would only want to see an address the first time it ever showed up, but not when that IP’s score increased or decreased. With Slack alerting you get an alert in all three cases, and it’s at least disconcerting to have them work differently.
Now we send an alert to Slack and Syslog when an IP first shows up, when its score increases, and when its score decreases. The threshold setting still applies, so you’ll only see alerts to Slack and Syslog for scores that exceed their respective thresholds.
Others
This release has some behind-the-scenes fixes and improvements too. In particular, the IP address details display shows up more quickly than in previous releases.
Release
The new software is in your customer portal account. For details on how to install it, please see the Install Guide.
Enjoy!
-Bill

Bill has authored numerous articles and tools for client use. He also serves as a content author and faculty member at the SANS Institute, teaching the Linux System Administration, Perimeter Protection, Securing Linux and Unix, and Intrusion Detection tracks. Bill’s background is in network and operating system security; he was the chief architect of one commercial and two open source firewalls and is an active contributor to multiple projects in the Linux development effort. Bill’s articles and tools can be found in online journals and at http://github.com/activecm/ and http://www.stearns.org.